OAuth 2.0 Migration: Security Best Practices
OAuth 2.0 Migration: Security Best Practices
OAuth 2.0 is a modern authentication framework that replaces outdated methods like password sharing and static API keys, often found in legacy Twitter API alternatives. It improves security by using short-lived access tokens and granular permissions, ensuring apps don't handle user credentials directly. However, migrating to OAuth 2.0 introduces risks like token theft, misconfigurations, and redirect vulnerabilities, which need careful handling.
Key points for a secure migration:
- Enforce PKCE (Proof Key for Code Exchange) to prevent code interception.
- Use short-lived tokens with narrow scopes and implement refresh token rotation.
- Secure token storage using
HttpOnlycookies or secure platform-specific storage. - Validate redirect URIs strictly - no wildcards or partial matches.
- Transition from deprecated flows, like Implicit and Resource Owner Password Credentials, to the Authorization Code Flow with PKCE.
- Monitor token usage and log authentication events to detect anomalies.
Platforms like Google and Microsoft are already phasing out older methods, with deadlines in 2025 and 2026. To stay secure, follow the latest OAuth 2.1 and RFC 9700 guidelines, which address common vulnerabilities and mandate safer practices.
OAuth 2.1 & PKCE: The New Standard [Advanced Backend & Security]
sbb-itb-9cf686c
Security Risks in OAuth 2.0 Implementations
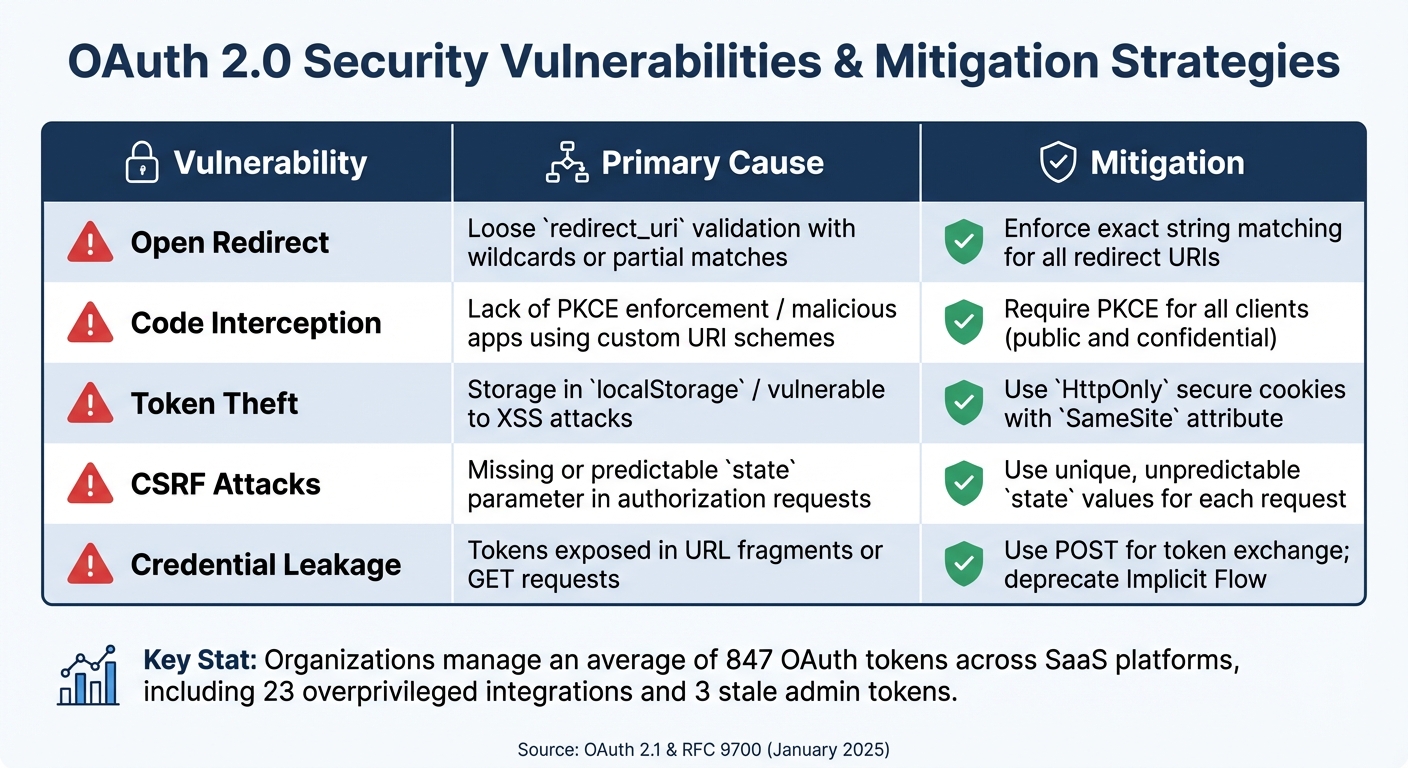
OAuth 2.0 Security Vulnerabilities and Mitigation Strategies
OAuth 2.0 has undeniably improved authentication processes, but its effectiveness can be undermined by poor implementation. Most vulnerabilities arise not from the protocol itself but from misconfigurations or overlooked security measures. Recognizing these risks is critical for avoiding mistakes and ensuring a secure OAuth 2.0 setup.
Token Exposure and Mismanagement
Bearer tokens act as the keys to a user's account. If someone steals one, they gain full access without needing further authentication. A stark example occurred in July 2025, when attackers used malicious OAuth apps to compromise Allianz Life's Salesforce systems, exposing 1.1 million customer records.
"OAuth tokens bypass MFA by design: Once granted, bearer tokens provide access without re-authentication, making token theft and consent phishing more dangerous than credential compromise." - Obsidian Security
Storing tokens in browser storage is a risky move, as they become vulnerable to cross-site scripting (XSS) attacks. Tokens can also leak through browser history or Referer headers if included in URL parameters - one reason the Implicit Flow is now deprecated.
Refresh tokens present even greater risks. Unlike access tokens, which expire quickly, refresh tokens can last for months. Research shows organizations manage an average of 847 OAuth tokens across SaaS platforms, including 23 overprivileged integrations and 3 stale admin tokens. If refresh tokens are stolen and not rotated or bound to a specific client, they can provide unauthorized access for weeks without detection.
These issues underline the importance of strict token validation, which ties directly into the next vulnerability.
Open Redirect URI Vulnerabilities
Misconfigured redirect URIs are a common weak spot, allowing attackers to intercept authorization codes during the OAuth flow. This happens when authorization servers accept overly flexible patterns - such as wildcards, partial path matches, or subdomain variations - rather than enforcing exact string matches.
Here’s how attackers exploit this: They create a malicious authorization request with a redirect_uri pointing to their server. If the authorization server doesn’t strictly validate the URI against a pre-approved whitelist, it sends the authorization code to the attacker. Silent authentication flows, using parameters like prompt=none, make these attacks even harder to detect.
"OAuth specifications, including RFC 6749, define how authorization errors are handled through redirects... attackers can deliberately trigger OAuth errors, such as by using invalid parameters like
scopeorprompt=none, to force silent error redirects." - Microsoft Defender Security Research
This risk becomes more pronounced during migrations, as organizations may allow flexible redirect URIs to accommodate legacy systems. In November 2024, a vulnerability in Tumblr’s logout endpoints highlighted how insufficient validation can lead to open redirect attacks.
Authorization Code Interception
Mobile apps face a unique challenge: malicious apps registering the same custom URI scheme as legitimate apps to intercept authorization codes. If Proof Key for Code Exchange (PKCE) isn’t enforced, attackers can exchange intercepted codes for access tokens. Even when PKCE is supported, phased migrations may leave room for downgrade attacks if servers don’t enforce it.
| Vulnerability | Primary Cause | Mitigation |
|---|---|---|
| Open Redirect | Loose redirect_uri validation |
Enforce exact string matching |
| Code Interception | Lack of PKCE / custom URI schemes | Require PKCE for all clients |
| Token Theft | Storage in localStorage / XSS |
Use HttpOnly secure cookies |
| CSRF | Missing or predictable state parameter |
Use unique, unpredictable state values |
| Credential Leakage | Tokens in URL fragments/GET requests | Use POST for token exchange; avoid Implicit Flow |
These vulnerabilities have driven significant changes in OAuth standards. For instance, RFC 9700, published in January 2025, mandates PKCE for all public clients and officially deprecates insecure flows like the Implicit Grant. Addressing these risks is essential for a secure migration, as explored in the next section on best practices.
Security Best Practices for OAuth 2.0 Migration
Migrating to OAuth 2.0 demands a careful focus on security at every stage. This approach addresses the vulnerabilities previously discussed. Newer standards like OAuth 2.1 and RFC 9700 (released in January 2025) bring together years of lessons into actionable steps.
Enforce PKCE for Public Clients
To prevent authorization code interception, PKCE (Proof Key for Code Exchange) should be enforced for all clients. Initially designed for public clients, PKCE is now mandatory for confidential clients as well. It safeguards the authorization process by binding the authorization request to the token exchange using a SHA-256 hashed code verifier.
When exchanging the authorization code for tokens, the app must include the original verifier. Without it, the exchange fails, blocking potential interception attacks.
"PKCE is no longer just a best practice for public clients; it's now mandatory for all applications, including confidential clients like server-based apps." – Maria Paktiti, WorkOS
Always use the S256 method for code challenges. Avoid the "plain" method, as it sends the verifier in an unprotected format, defeating PKCE's purpose. For added security:
- Generate a unique verifier for every authorization request to prevent replay attacks.
- In web apps, store the verifier in
sessionStorageto reduce exposure.
PKCE also allows for the deprecation of the Implicit Flow, which is no longer recommended in OAuth 2.1. The Implicit Flow exposed access tokens in browser URLs, making them vulnerable to leaks via history or referrer headers. Instead, the Authorization Code Flow with PKCE is now the standard for all client types.
Use Short-Lived and Scoped Tokens
Access tokens should have a short lifespan - ideally expiring within 15–30 minutes. Each refresh should invalidate the previous token, which helps detect and mitigate theft. If a stolen refresh token is reused, it signals a compromise and should trigger revocation of all tokens for that session.
Tokens should also follow the principle of least privilege. Instead of requesting broad permissions like admin, define narrowly scoped permissions such as read:profile or write:tweets. This reduces potential damage if a token is compromised.
"Security decisions need to be deliberate, covering how tokens are issued, validated, transmitted, and revoked." – Fung, Product Manager, Authgear
For even greater protection, use sender-constrained tokens with technologies like DPoP (Demonstration of Proof-of-Possession) or mTLS (mutual TLS). These methods bind tokens to specific clients, ensuring stolen tokens cannot be used without the corresponding private key or certificate.
Secure Token Storage and Transmission
Proper token storage and secure transmission are key to preventing unauthorized access. For web applications:
- Use
HttpOnly,Secure, andSameSitecookies:HttpOnlyblocks JavaScript access.Secureensures tokens are sent only over HTTPS.SameSitemitigates cross-site request forgery.
For single-page applications (SPAs), consider the Backend for Frontend (BFF) pattern. In this setup, the SPA communicates with a server-side proxy that handles OAuth flows and token management. The proxy then issues secure cookies to the frontend, keeping tokens out of the browser environment entirely.
For mobile apps, rely on platform-specific secure storage:
- Use the iOS Keychain for iOS.
- Use Android Keystore or Encrypted SharedPreferences for Android.
Server-side applications should store tokens securely using memory-only storage, encrypted databases, or protected environment variables.
Finally, ensure all OAuth interactions occur over HTTPS/TLS to prevent interception. According to the 2024 Verizon Data Breach Investigations Report, 86% of breaches involved stolen credentials, including OAuth tokens and API keys.
When configuring redirect URIs, enforce exact string matching. Avoid using wildcards or partial matches, as these can create open redirect vulnerabilities, allowing attackers to intercept authorization codes. Authorization servers should reject any redirect URI that doesn't exactly match a pre-registered value.
Planning and Executing Your Migration
With strong security measures in place, careful planning is key to a smooth OAuth 2.0 migration. While most organizations complete the process in three to six months, a focused effort can achieve core security upgrades in as little as six weeks.
Assess Current Authentication Flows
Start by documenting all existing OAuth implementations, focusing on token usage and transmission methods. Catalog each OAuth flow - such as implicit, authorization code, client credentials, and ROPC - and examine how tokens are being transmitted. Pay close attention to tokens sent via headers, query parameters, or POST bodies, and flag any tokens appearing in URLs.
Next, review all registered redirect URIs and prepare for exact string matching. Simple mismatches in redirect URIs - like extra slashes or inconsistent capitalization - account for 40% of authorization failures. Check your authorization server’s compliance with OAuth 2.1 and RFC 9700, which was published in January 2025. If you’re still using the Implicit Flow or ROPC, prioritize their removal immediately.
Phased Migration and Compatibility Testing
Implement changes step by step, starting in development environments. Use separate OAuth client configurations for development, staging, and production to prevent accidental overlaps. A six-week phased timeline might look like this:
- Week 1: Remove implicit flows and stop sending tokens in query parameters.
- Weeks 2-3: Add PKCE (Proof Key for Code Exchange) to authorization code flows and enforce strict redirect URI matching.
- Weeks 4-6: Introduce refresh token rotation and transition to discovery endpoints.
"OAuth 2.1 eliminates vulnerability classes that attackers actively exploit in OAuth 2.0 implementations." – Ashur Kanoon, Technical Product Marketing, Aembit
Feature flags are incredibly useful for rolling out changes gradually in production. This allows you to test each phase with limited traffic. Keep a close eye on authentication failure rates - spikes could indicate breaking changes that affect users. Ensure your authorization server processes refresh requests atomically, issuing new tokens before invalidating old ones to prevent race conditions. Always have a rollback plan in place in case critical issues arise during deployment.
Monitoring and Post-Migration Security Checks
Once the migration is complete, ongoing monitoring is critical to maintaining security. Log every authentication event and track configuration changes to avoid security drift or automated request errors. Watch for refresh token reuse - an invalidated token being used could signal an attempted account takeover. Similarly, track authorization code reuse; if the same code is used more than once, revoke all related tokens immediately.
"By issuing new refresh tokens and rotating them every time a token is used, the tokens can be made one time use and attempts to use the wrong token can be flagged and recorded, making this a very powerful protection against silent account takeover." – Phil Condon, Security Consultant, Sentrium Security
Regularly validate tokens for expiration, issuer (iss), audience (aud), and cryptographic signature integrity. Use unique token identifiers (jti) to detect replay attacks. Conduct periodic penetration tests to uncover any vulnerabilities that may have been overlooked during the migration. This is especially important, as 42% of API failures often go unnoticed.
Conclusion
Security Practices Recap
Migrating to OAuth 2.0 requires a thorough review of your security measures. Key updates include making PKCE mandatory for all client types, even confidential server-side apps. The Implicit Grant and Resource Owner Password Credentials flows should be retired immediately, and strict string matching for redirect URIs must be enforced to avoid open redirect vulnerabilities. Refresh token rotation is another essential step - each refresh token should be replaced upon use, invalidating the previous one.
"Setting up OAuth 2.0 for APIs isn't just ticking off some compliance checkbox - it's building a foundation of trust that users and partner developers will actually appreciate." – Zuplo
Short-lived access tokens, ideally lasting 15 to 30 minutes, significantly reduce the risk window for attackers. For Single-Page Applications (SPAs), adopt the Backend for Frontend (BFF) pattern. This approach stores tokens in HttpOnly cookies, keeping them out of reach from browser-based attacks. To further improve token security, implement sender-constrained tokens using DPoP or mTLS, ensuring tokens are bound to specific clients and can't be reused if stolen.
By applying these measures, you're not just securing your current setup - you’re laying the groundwork for a system that can adapt to future threats.
Next Steps for Secure Authentication
OAuth security isn’t a one-and-done task - it requires constant vigilance. New threats, like Audience Injection and Cross-toolkit OAuth Account Takeover, continue to emerge. To address these, the latest update to the OAuth 2.0 Security Best Current Practice was released on March 2, 2026. Consider this: attackers can exploit a refresh token breach within 30 minutes, yet it often takes security teams over 5 hours to detect such incidents.
"Your strongest authentication controls are irrelevant once an attacker holds a valid refresh token." – Obsidian Security
To stay ahead, deploy behavioral monitoring to catch anomalies like sudden API call spikes or unusual geographic access. Regularly audit your OAuth applications to revoke unused or overly permissive integrations. Token lifetimes also matter - limit SPAs to 24 hours at most, while sensitive server-side applications should have tokens lasting no more than 7 to 30 days. Keep up with RFC updates and security advisories as the standards evolve toward OAuth 2.1 and beyond. Regular audits and proactive updates are your best defense against the ever-changing security landscape.
FAQs
How do I choose the right OAuth flow for my app type (web, SPA, mobile, server)?
The right OAuth 2.0 flow will vary based on your app's structure and the level of security required:
- Web apps: The Authorization Code flow, combined with PKCE, provides an extra layer of security.
- Single-page applications (SPAs) and mobile apps: Using the Authorization Code flow with PKCE ensures tokens are less vulnerable to interception.
- Server-to-server apps: The Client Credentials flow works best since it doesn't involve user interaction.
It's recommended to avoid using implicit grants for new applications because of known security risks.
What’s the safest way to store access and refresh tokens without exposing them to XSS or leaks?
To protect access and refresh tokens, steer clear of storing them in browser storage such as localStorage or sessionStorage. A safer approach is to store tokens on the server side and send them using secure, HTTP-only cookies with the SameSite attribute enabled. This method helps block malicious scripts from accessing the tokens and minimizes the risk of leaks or cross-site scripting (XSS) attacks.
How can I detect and respond to refresh-token reuse or stolen tokens in production?
To spot refresh-token misuse, keep an eye out for red flags like impossible travel scenarios, inconsistent device usage, or unusual access patterns. Strengthen security by adopting token binding techniques such as Proof of Possession (PoP) or mutual TLS (mTLS). Additionally, set up automated workflows to swiftly detect, respond to, and revoke compromised tokens, helping to maintain the integrity of your system with minimal disruption.
Tags
Ready to get started?
Try TwitterAPI.io for free and access powerful Twitter data APIs.
Get Started Free